Access Control & Intrusion Detection
Unauthorized Access Detection in Restricted Areas
When an unauthorized worker approaches or enters a designated security zone,
it immediately detects and notifies to preemptively block access regulation violations.
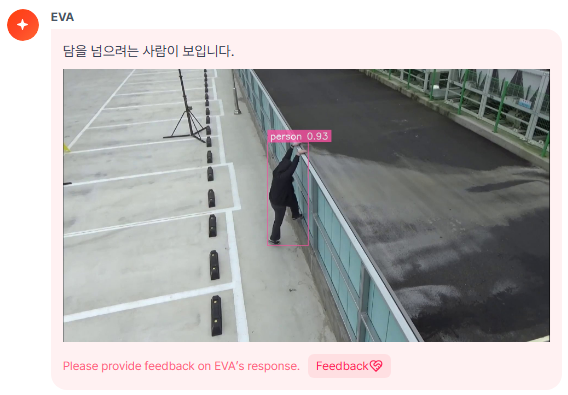
Climbing Intrusion Detection
Detects abnormal access such as crossing physical boundaries like walls or fences in real-time,
supporting immediate response from security personnel in case of external intrusion.
Suspicious Behavior & Loitering Detection
Automatically identifies abnormal behaviors such as repeated loitering or lingering around facilities,
allowing for early identification of potential security threats and providing advance warnings.
Only 5 minutes to turn a normal camera into an AI camera! This is how it went.

Setting Detection Scenarios
Easily write detection conditions with prompts.
e.g., "Detect people climbing the wall"
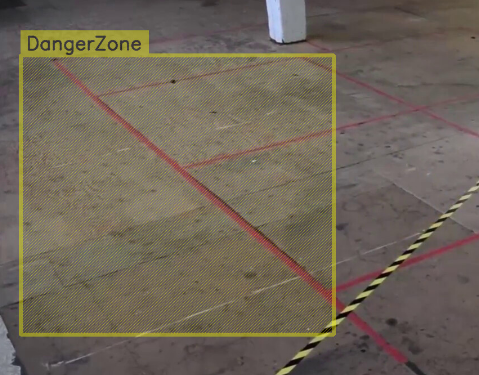
Area Setting
Please set the area for danger zones.
Detection is performed for that area.
Check Results & Optimize
Check detection results and modify areas and scenarios if necessary.
Preemptive Blocking of Security Threats
Intrusion into industrial facilities can cause significant damage such as theft, equipment damage, and operational stops.
EVA identifies risk factors early and establishes a rapid response system through
access control in restricted areas and real-time monitoring of intrusion situations.
Automatic Response Through Security System Integration
EVA goes beyond simple video monitoring and integrates with access gates, alarm devices, and lighting control to
perform immediate automatic security actions such as blocking, warning, and tracking when an intrusion occurs.
This implements a Physical Security environment that strengthens facility safety.